What is IT auditing?
An IT audit is a thorough assessment of the management systems and operatives within an IT infrastructure. The evaluation of thus obtained data determines if the information systems are securing assets, holding data integrity, and operating effectively without any compromises to achieve the organization’s goals or objectives. These reviews may be performed featuring a financial statement audit, internal audit, or other forms of an attestation engagement. IT audits are also known as automated data processing audits (ADP audits) and computer audits
What is the purpose of an IT audit?
An IT audit and a financial audit may both serve the same values, but functional wise they both are quite different from each other. A financial audit’s mandate is to evaluate whether the financial statements are presented fairly, an institution’s financial position, the results of operations in terms of finance, and the standard monetary and fiscal policies of the institution. The mandate of an IT audit is to examine and evaluate appropriately the system’s internal control design and effectiveness. This includes, the efficiency and security protocols, development processes, and IT governance or oversight. Installing control checks are necessary but not sufficient to ensure adequate security. People responsible for the security must consider if the systems are installed properly as mandated, if they are effective, or if any breach in security has occurred and if so, what immediate plan of action can be implemented to safeguard the present systems from the current compromise and also prevent future breaches. These questions should be answered and the solutions implemented by independent and unbiased observers that take no stake in the organization. These observers perform the task of IS auditing. In an IS environment, an audit is an examination of information systems, their inputs, outputs, and processing.
The primary functions of an information technology audit are to evaluate the systems that are in place to guard the integrity of an organization’s information. Specifically, IT audits are used to evaluate the organization’s ability to protect its information assets and to properly dispense information to authorized parties. The IT audit aims to evaluate the following:
Will the organization’s IT and IS be available for the business at all times when required – availability? Will the information in the systems be disclosed only to the authorized users? – security and confidentiality. Will the information provided by the system always be accurate, reliable, and timely – measures integrity? In this way, the audit hopes to assess the risk to the company’s valuable asset and establish methods of minimizing those risks.
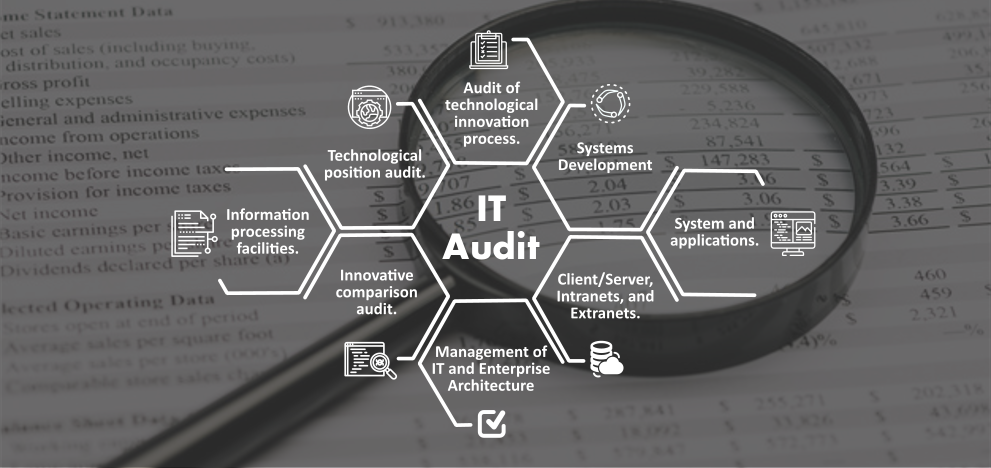
What are the different types of IT audits?
Based on systematic approaches to carry out an IT audit, there are three types of IT audits:
Audit of technological innovation processes:
This audit creates a risk index for present and future projects. The audit will assess the magnitude of the company’s experience in its current operative systems, as well as its presence in the relevant markets, the organization of each project, and the generalized arrangement of the portion of the industry that deals with this project or product, organization and industry structure.
Innovative comparison audit:
This assessment is an in depth analysis of the innovative abilities and capabilities of the company being audited, in comparison to its competitors in the industry. This requires a thorough analysis of company’s research and development facilities, as well as its track record in actually producing new products.
Technological position audit:
This audit reviews the technologies that the institution currently owns and that it needs to add. Technologies are characterized as being either bases, keys, pacings or emergings.
Based on the hosting functionality and process, IT auditing can be of five types:
Systems and Applications:
An inspection to verify that the systems and its applications are appropriate, optimal, and secure to ensure proper input, processing, and output at without any compromises in any and all aspects.
Information Processing Facilities:
An assessment to make sure that the processing unit is controlled to ensure proper processing of applications and data under normal and potentially disruptive conditions.
Systems Development:
An audit to verify that the systems under development meet the objectives of the organization, and to ensure that the systems are developed in accordance with generally accepted standards for systems development.
Management of IT and Enterprise Architecture:
An assessment to ensure whether that information technology management has developed a system of organized structures and procedures to ensure a controlled and efficient environment for information processing.
Client/Server, Telecommunications, Intranets, and Extranets:
An assessment to make sure that the telecommunications systems are in place on the client server, and on the network connecting the clients and servers.